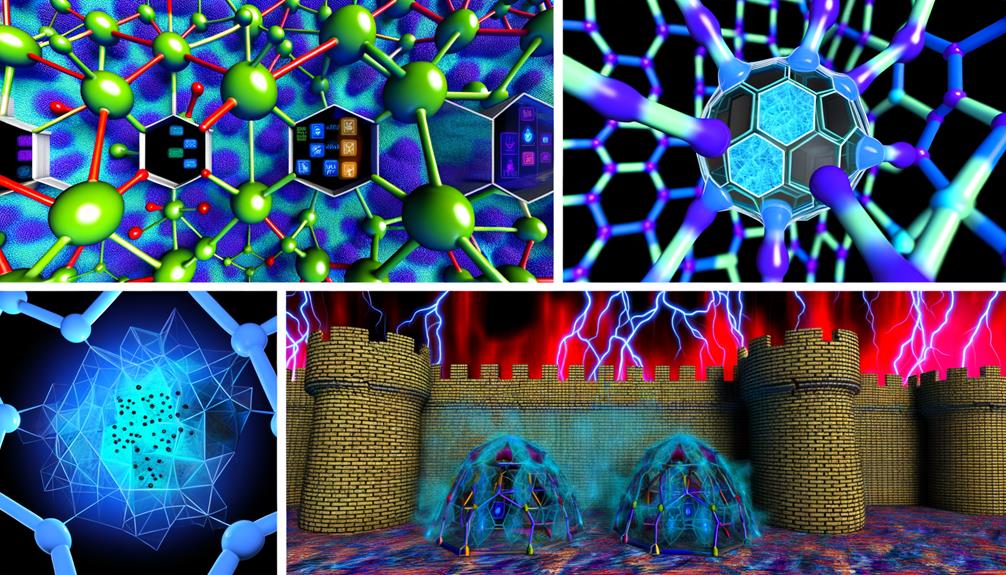
By integrating artificial intelligence into threat management, I revolutionize my cybersecurity strategies with proactive, predictive measures that swiftly analyze vast amounts of data for early warnings and enhance incident response, shifting my security approach from reactive to proactive. This cutting-edge approach leverages AI-powered tools and advanced algorithms such as machine learning, dimensionality reduction, and K-nearest neighbors to bolster threat detection, streamline response times, and fortify my organization's defenses. Going forward, I'll uncover more innovative ways to transform security with data-driven insights.
Key Takeaways
- AI-powered predictive defense enhances cybersecurity with proactive tactics, analyzing vast data for early warnings and enabling resilient security measures.
- Advanced algorithms like machine learning and dimensionality reduction enhance threat detection, response, and authentication.
- AI in threat intelligence management automates threat detection for faster responses, providing strategic insights for proactive defense.
- Streamlined threat response with AI reduces reaction times by up to 90% through automation and advanced analytics.
- AI for anomaly detection learns from evolving threats, detects subtle deviations, and triggers automated protective measures to strengthen security posture.
Harnessing AI for Predictive Defense
Harnessing AI for Predictive Defense
Incorporating AI-powered predictive analytics into our cyber defense enables us to effectively gamble on potential threats, anticipating and mitigating risks before they strike. This proactive tactic guarantees that our security posture is fortified and adaptable to the evolving nature of cybercrime.
Deep learning algorithms in AI can swiftly analyze vast amounts of data to identify patterns and anomalies in real-time, providing early warnings and actionable insights to prevent security threats before they materialize. This predictive defense allows us to be proactive and take preventive measures, enhancing our security resilience and adaptability in the face of these threats.
Leveraging AI for predictive defense offers precise security measures by detecting anomalies and future threat patterns. It revolutionizes our approach to security by shifting from reactive to proactive, thereby safeguarding sensitive data and preventing potential breaches with unparalleled efficiency.
With AI-powered predictive analytics, we can see what may come and act accordingly, ensuring a secure environment that grants us the freedom to operate without fear of interference.
Advanced Algorithms for Proactive Security
As we integrate advanced algorithms into our security analytics, we can greatly enhance our ability to proactively thwart cyber threats before they materialize. This integration offers us a significant advantage in staying ahead of evolving threats and protecting our systems more effectively.
Key Features of Advanced Algorithms in Security Analytics
| Algorithm | Use Case | Benefits |
|---|---|---|
| Machine Learning | Anomaly Detection | Enhanced threat identification |
| AI | Predictive Defense | Improved incident response |
| Dimensionality Reduction | Data Noise Filtering | Better data accuracy |
| K-Nearest Neighbors (KNN) | Facial Recognition | Improved authentication |
| Random Forest | Phishing Attack Classification | Enhanced threat classification |
AI in Threat Intelligence Management

As we examine how AI revolutionizes security analytics, I want to highlight how AI automates threat detection, enhancing our incident response capabilities and providing key insights into strategic threat intelligence.
AI's ability to streamline the threat detection process allows for faster and more accurate responses to emerging threats. By automating this process, we can focus on high-level threat analysis and strategic decision-making.
AI Automates Threat Detection
AI-powered threat intelligence management empowers organizations to proactively respond to emerging threats by automating threat detection through real-time analysis of vast amounts of data, greatly enhancing defense strategies. By leveraging advanced machine learning and AI algorithms, security teams can efficiently sift through enormous volumes of data, identifying patterns and anomalies that signal potential threats. This automation enables the swift detection of security risks, allowing organizations to respond promptly and effectively mitigate potential damage.
The accuracy and efficiency of AI-driven analytics revolutionize traditional threat detection methods. No longer do security analysts need to manually review vast logs or network traffic. AI takes care of this task, freeing up valued resources to focus on more critical investigations. Additionally, AI algorithms can predict potential threats based on historical data and trends, enabling organizations to proactively fortify their defenses.
With AI automating threat detection, security teams can shift from reactive to proactive defense strategies, staying ahead of cyber threats and ensuring a safer digital environment.
Enhancing Incident Response
By harnessing the speed and precision of AI-driven analytics, my organization can greatly improve incident response, fortifying defenses against rapid-fire threats and vulnerabilities.
AI in threat intelligence management improves our response by leveraging machine learning algorithms to rapidly detect and respond to potential threats. This integration enables real-time insights into emerging threats, providing a proactive defense against malicious activities.
Advanced analytics also help reduce false positives, prioritize critical vulnerabilities, and streamline incident response processes.
With AI-powered threat intelligence, we can revamp our security strategy by providing deeper insights and enabling quicker threat mitigation. This transformation allows us to maximize the value of our data and enhance our overall security posture.
Strategic Threat Insights
In threat intelligence management, leveraging AI's real-time data analysis capabilities revolutionizes our ability to proactively defend against emerging cyber threats. By utilizing AI-powered threat intelligence feeds, we gain actionable insights to anticipate potential attacks. The advanced analytics involved in threat intelligence management streamline our security posture assessment, allowing for swift responses to threats. Furthermore, the integration of AI algorithms improves the accuracy of identifying critical vulnerabilities, enabling informed decisions on strengthening our defenses.
With strategic threat insights, our security strategy evolves dynamically. These advanced insights empower us to develop thorough strategies to combat emerging threats before they become major breaches. Additionally, we can direct our resources more effectively, focusing on the most pressing vulnerabilities while staying a step ahead of potential attackers.
Enhancing Efficiency With Automation
In my quest to optimize security infrastructure, I've been observing how automation plays a significant role in streamlining our threat response.
Through AI-enhanced threat detection and smart security integration, we can eliminate manual tasks that eat into our efficiency.
AI-Enhanced Threat Detection
For me, a transformative pillar in modern cybersecurity is AI-boosted threat detection. This technology expedites the process of identifying potential security risks in real-time. Advanced analytics powered by AI greatly enhances efficiency in threat detection and response. The automation through AI reduces the burden on human analysts and allows for faster threat mitigation. By leveraging the power of AI in threat detection, organizations can stay ahead of evolving cyber threats and adopt proactive security measures.
The use of AI-boosted threat detection systems enables the rapid analysis of vast amounts of data, enhancing the overall security posture. This technology can identify patterns and anomalies that traditional methods might overlook, ensuring swift action against potential threats. Additionally, AI enhances threat intelligence by enriching collected information with valuable context and metadata, such as geolocation and timestamps, providing a thorough understanding for informed security decisions.
With AI-boosted threat detection, organizations can fortify their security defenses and better navigate the ever-evolving threat landscape.
Automation in Threat Response
Improving efficiency in threat response is crucial, and automation greatly leverages our security capabilities by streamlining responses and reducing reaction times. By adopting automation in threat response, we can reduce response time by up to 90%. This means we can react more swiftly to emerging threats, minimizing their impact on our operations.
Automation can handle up to 80% of routine security tasks, freeing our security teams to focus on more strategic and complex issues. Additionally, automated threat response can save organizations up to $1.5 million annually by optimizing resource allocation and reducing the workload of our security personnel.
According to recent statistics, security automation can address 70% of security incidents without human intervention, allowing us to respond swiftly and effectively.
Smart Security Integration
By integrating state-of-the-art analytics with security systems, we can greatly enhance our security stance through automation, effectively detecting threats in real-time and proactively neutralizing them. This intelligent security integration streamlines the monitoring and management of security incidents, enabling quicker resolution and mitigation. Automation of security tasks through advanced analytics minimizes human error and improves overall security efficiency.
| Benefits | Implementation |
|---|---|
| Enhanced Efficiency | Automation of Routine Tasks |
| Real-time Threat Detection | Integration of Analytics Tools |
| Proactive Defense | Minimized Human Error |
| Strategic Focus | Advanced Analytics Capabilities |
Through automation, we can respond to threats more rapidly, reducing the need for manual intervention and response times. This frees security teams to focus on strategic initiatives and thorough threat analysis rather than routine tasks. By leveraging smart security integration, we can revolutionize our security operations and ensure a safer, more liberated digital landscape.
AI for Anomaly Detection and Response

In the field of digital security, the contrast between anomaly detection and the proactive identification of potential threats can be a matter of seconds. Today, cutting-edge analytics enables the creation of AI-powered anomaly detection systems that dissect massive volumes of data in real-time, identifying unusual patterns or behaviors that deviate from the norm. These advanced systems are able to detect even the most subtle deviations from normal activity, allowing security teams to respond swiftly to potential threats.
By leveraging AI for anomaly detection and response, we can greatly enhance our security posture. AI algorithms continuously learn and adapt to evolving threats, ensuring that anomaly detection improves in accuracy over time. This proactive approach empowers us to stay ahead of threats before they materialize, reducing the risk of costly downtime and security breaches.
The integration of AI in anomaly detection and response optimizes security operations by reducing false alarms and improving incident handling efficiency. With AI-driven systems, we can swiftly identify and respond to security incidents, mitigating harm before it escalates.
As we continue to harness the power of AI, we're better equipped to safeguard our digital infrastructure and secure our future.
Implementing AI for Active Risk Mitigation
To proactively mitigate risks, I must leverage AI's advanced analytical capabilities to detect threats in real-time, ensuring timely and effective responses to potential security breaches. This revolutionary approach empowers organizations to stay one step ahead of cybercriminals, safeguarding sensitive data and critical infrastructure.
Here are the key strategies I utilize to lock down vulnerabilities:
- Enhanced Anomaly Detection: AI-driven analytics scrutinize vast amounts of data to identify patterns indicative of anomalous behavior, alerting me to potential threats before they escalate.
- Proactive Response Mechanisms: I set up automated response systems that rapidly trigger protective measures upon threat detection, minimizing the attack surface.
- Continuous Monitoring: AI algorithms continuously assess the security landscape, ensuring timely detection of emerging risks and violations of security protocols.
- Adaptive Security Measures: Based on insights from AI analytics, I fine-tune security protocols, adjust access controls, and implement targeted threat countermeasures to strengthen the overall security posture.
Frequently Asked Questions
What Is Cutting Edge Technology in Cyber Security?
"In cybersecurity, cutting-edge technology involves leveraging advanced analytics, machine learning, and network monitoring to enhance threat detection. This includes behavioral analytics and real-time monitoring for proactive defense and adaptive response."
What Is the Application of Data Analytics in Security?
In security,ретtime monitoring allows for instant detection and response, while anomaly detection identifies unusual patterns. Predictive analysis forecasts potential threats, and threat intelligence enhances situational awareness—enabling proactive defense and fostering a safer, freer digital landscape.